Table of Contents
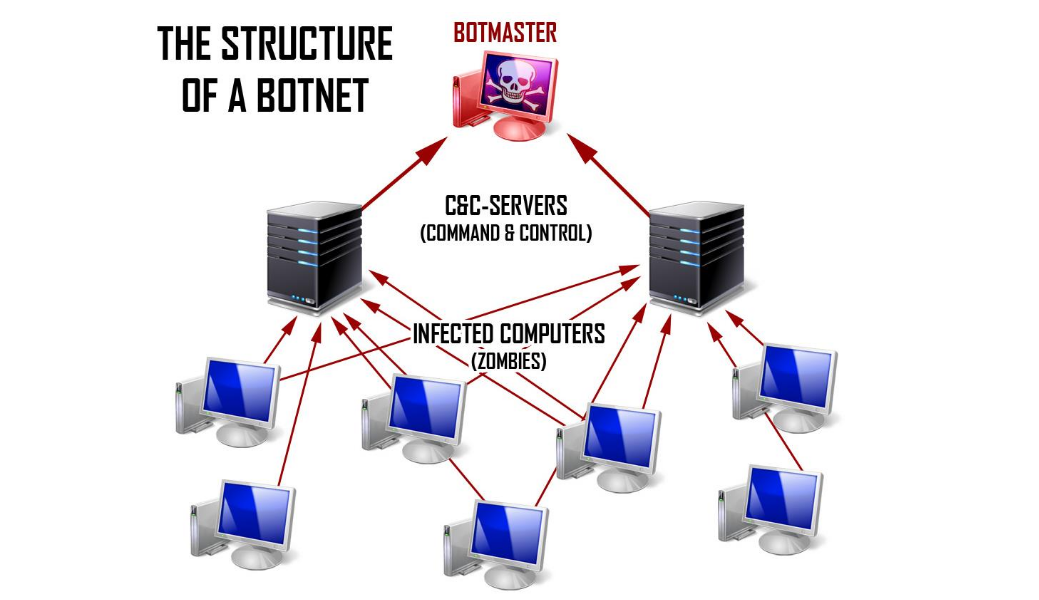
A botnet or network of bots is a computer network that consists of a vast quantity of computers that contain hidden deleterious software. This software lets you perform any activities remotely on your computer. Hundreds and thousands of contaminated computers, as a rule, are used for illegal activities on the web like mailing of spam, viruses, stealing of private data, and DDoS (Distributed Denial of Service) attacks. Today botnets are considered to be one of the most dangerous cyber threats.
Usually, these dangerous programs are distributed in strange emails and downloads from the internet, like fake files or programs. Also, intruders work through outdated software and the absence of protection from viruses on your computer. Now they are going further and invading smartphones (cameras), smart TV, smart cars.
How does a botnet work?
Intruders who own botnets have access to a huge number of computers and can perform any activities on them; of course, all of them are malicious. Usually, cybercriminals use Trojan viruses to get access to computers. They try to make as many attacks simultaneously as possible.
Botnets can be called great platforms for cybercriminals as they bring a huge amount of illegal income. How do intruders act to get money from computer owners? Here are the most spread cases:
- quick and scalable distribution of emails that contain programs that extort money of users;
- a botnet can be a service that winds up tin clicks on the website;
- opening a proxy server for anonymous access to the internet;
- massive distribution of emails or hosting of fake websites;
- stealing of personal identifying data;
- theft of credit card, bank accounts information, including pin-codes and secret keys;
- installing a spy keyboard to record the data about everything that users type on the internet.
Types of botnets
Botnets attacks are supposed to be dangerous, as it is challenging to reveal them. There are several types of botnets, as they have different aims. They are the following:
DDoS or Distributed Denial of Operations Service
DDoS or Distributed Denial of Operations Service is mostly used for destroying the connections between networks and services. DDoS has different types of attacks, among them TCP SYN and UDP attacks. This malicious service can reach web servers and go further and invade all services connected to the internet. We want to mention the most scalable DDoS attack. This botnet used IoT-related Mirai virus.
The virus reached and controlled tens of thousands of less protected internet devices and turned them into bots to launch a DDoS attack. Mirai spawned many derivatives and continued to expand, making the attack more complex. It changed the threat landscape forever in terms of the techniques used.
Spam sending
However, DDoS attacks are not the most frequently used by botnets. One of the most popular ways of invading your computer is a mass email or spam. Although, it is not a simple annoying mail that you used to see before. It usually masks and looks like mail from a real company with strange files inside. When you open these files, you will launch a dangerous virus that will possess your computer and open access to private data. Also, there is another way of attacking your computer with spam. Intruders can send a mail with a malicious link to the website you know well and enter your login and password. This type is called phishing. Then your data can be scanned by intruders, and they will extort money to give it back.
Software vulnerabilities
This type of attack uses software errors and can have different ways of development. Using this type, intruders can get access to non-essential data or the whole control of your computer. This type of attack is considered to be the most frequently used.
Examples of Botnet Attacks
The world has seen several scalable attacks that are known all over the world. They were performed with the usage of very powerful botnets. So we prepared a list of the most famous hacker attack:
The 2018 GitHub Attack – In February 2018, a large botnet carried out the largest DDoS attack ever recorded. Generating peak incoming traffic of an unprecedented 1.35Tbps, the attack took GitHub, the largest software development platform on the internet, offline for a few minutes.
GitHub Attack
The 2014 Hong Kong Attack – The 2014 political unrest in Hong Kong provoked the then-largest DDoS attack in history when at least a few large botnets joined forces against pro-democracy websites. Many have accused the Chinese government of this attack, but the actual perpetrator remains unknown.
Hong Kong Attack
The 2016 Mirai Attack – Named after a popular anime series, Mirai was a botnet consisting of more than 100,000 computers. It made the news in 2016, when it launched attacks against several cybersecurity companies, generating traffic volumes of 1Tbps and taking down a large part of their online infrastructure.
Mirai Attack
Botnets for business
Despite the questionable reputation of botnets, it is not just about the cybercriminal. Today bots are used for the optimization of work processes in different business areas.
These days most companies build websites for a more efficient workflow. No matter your business industry, it is essential to protect your or your customers` private data.
Here comes the help of botnets that are used for your profit. Usually, developers use the same types of attacks to test the level of protection of your website. This process is called stress testing.
What is stress testing?
As we have already mentioned, stress testing is the process of testing your website’s resilience to hacker attacks. It shows how your website works with different levels of loads.
It is impossible to perform stress testing manually, so botnets are the perfect decision for this process as they generate huge requests. With the usage of botnets, you can reveal the weak sides of your development like:
- bottlenecks of the website or application
- absence of the right limitation of memory usage
- errors of code sync
- errors of loads balance
Types of stress testing
The most efficient way of testing your development is a DDoS attack. This type is a constant danger for modern businesses, and if your company is not prepared, you can be easily invaded by intruders. For performing this attack, they use IP stress tests to launch them.
To make it profitable for business, you also can use these botnets for testing your network. It helps you to know if your website is strong enough to cope with these attacks, or it is worth working better on the level of protection.
Here is the list of IP stress tests that can help you to avoid DDoS attacks in the future:
- Str3ssed Booter
It is the best choice for stress testing. IP Booter supports bandwidth up to 500Gbps thanks to dedicated services and web interface. - Free IP Stress
A free test that can run a stress test without any registration. - Free Stresser
An online tester supports up to 1Gbps spoof traffic and can run stress tests via a web page. - MuxBooter
A free network stress tester that can simulate application-level attacks using machine learning. - XYZ Booter
Thi tool has support for over 25 attack types with 10Gbps bandwidth per attack, which automatically deletes log data. - DOS Ninja
This is testing software that supports up to 1000 Gbps tests with Layer 4 and Layer 7 attacks. - Undisclosed.to
Stress testing tool compatible with Level 4 and Level 7 DoS attacks, with cryptocurrency for anonymity.
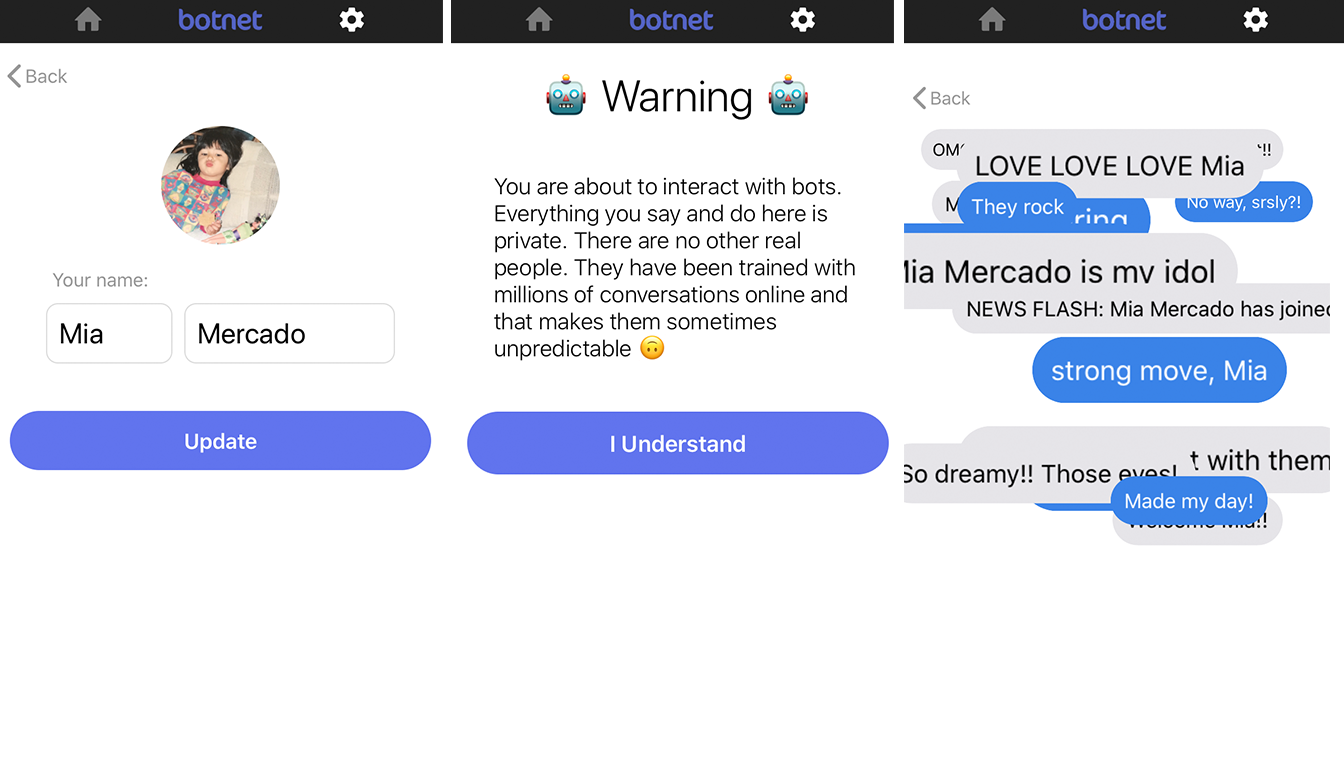
Botnet social media
The development of botnets doesn’t standstill. This year Billy chain, developers created a new social media called “Botnet.” It is a virtual world where there is the only real user – you. This social network is full of bots that adore your every post – picture, text, everything. It is a perfect world without haters and angry people.
The aim of building this type of social media is to make people feel needed and not lonely. Every user who installs this application gets constant interactions, likes, and comments under the posts, and they are complimentary.
Moreover, you can choose the way you will be praised. This social network is free, but you can buy a particular direction of comments – troll bots, dad bots, or doubled bots. In the era of digital technologies and many bloggers on social media, Botnet can become very popular as not all active social users can cope with hate online.
How to build a botnet?
To build a botnet, you don’t need much time, money, and effort. You can create it within 15 minutes. There are only three steps to do:
- choose a builder online
- build your payload – GUI interface to build the executable malware file
- set up your CnC infrastructure to control other computers
However, to build a botnet that will optimize your business’s work, you need to make more efforts. Your botnet has to be customized and has an individual approach to your case. This is possible only with the help of professionals.
How to choose a company to build a botnet?
When you are ready to hire specialists for building a botnet, you need to be sure that they have real experience in this field. You can easily understand it during the first consultation with a Business Analyst. It is the person that helps you to reveal the weak sides of your website or application and find ways to solve them. Aso, communication and individual approach are crucial.
Most people think that hiring a freelance developer is much better, faster, and less expensive. We covered the difference between freelancers and professional teams of developers.
| TEAM OF DEVELOPERS | FREELANCERS |
| The team consists of specialists in different areas, and all of them combine their knowledge to produce a product | Mostly, a freelancer is a specialist in one field, and if you want to build the whole project, you will need more than 1 person, it may be much more expensive than to hire a team |
| Hiring a team implies accurate documentation, estimations, deadlines, etc. | Freelancer can give you only an oral reprimand and don’t keep it if he wants |
| The team is focused on your project and keep constant communication. | Freelancers can have several different projects and won’t concentrate on the best way. |
| The team is always managed by a responsible employee who keeps the timing, controls quick replies, keeps in touch with the client. | Freelancer is granted to himself and doesn’t often care about the difference in time and keeping in touch with the client about every update. |
| The team has an individual approach to every customer, reveals his/her requirements and desires to build the solution that the customer wants to see as the final result. | Freelancer can add some features that he thinks would be suitable without customer agreement; it can lead to poor communication and failed projects. |
Conclusion
Taking into account both sides of botnets, the aim of creating bots depends only on you. Most people used to think that botnets are malicious tools to steal private data from their computers. However, now the situation is changing. Bots can help businesses in all areas to make their work processes more productive and efficient. There are so many different types of bots that can help you with your company. Bots help your employees cope with a huge amount of work like orders, services, and customer communication. They make the customer’s experience excellent. Therefore, the need for many employees reduces, and the customers and income are increasing. If you want to know how bots can improve your workflow, you need to contact specialists who will recommend and build an individual business strategy for your company.